COVIDSafe: Australia’s digital contact tracing failure
I'm here all by myself reading actual peer-reviewed publications from other countries where appropriate technology was rolled out to assist medical professionals whilst Australia remains in shambles.

2020 was a year that I will never forget. Early February I was camping in the woods with a bunch of hippies without a care in the world meanwhile on the outside everyone in Babylon was starting to lose their collective shit.
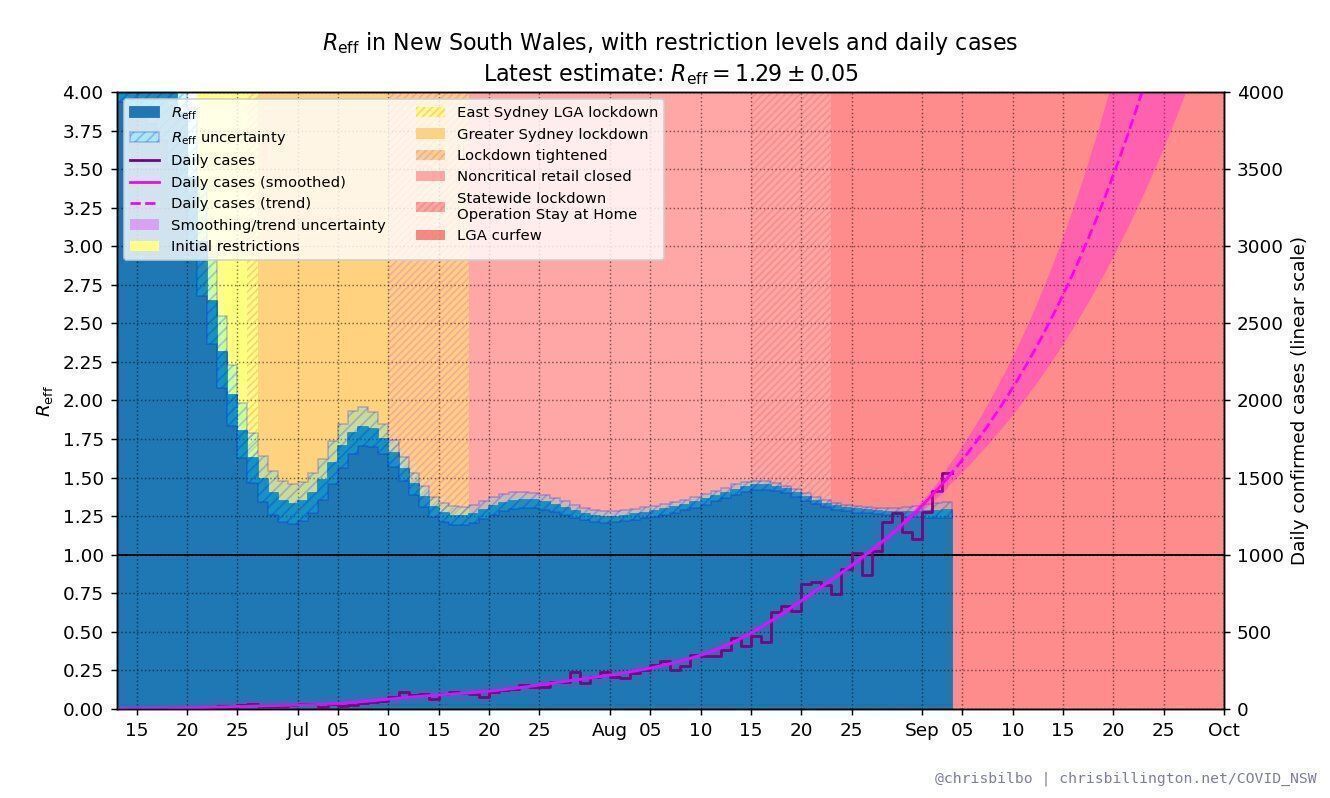
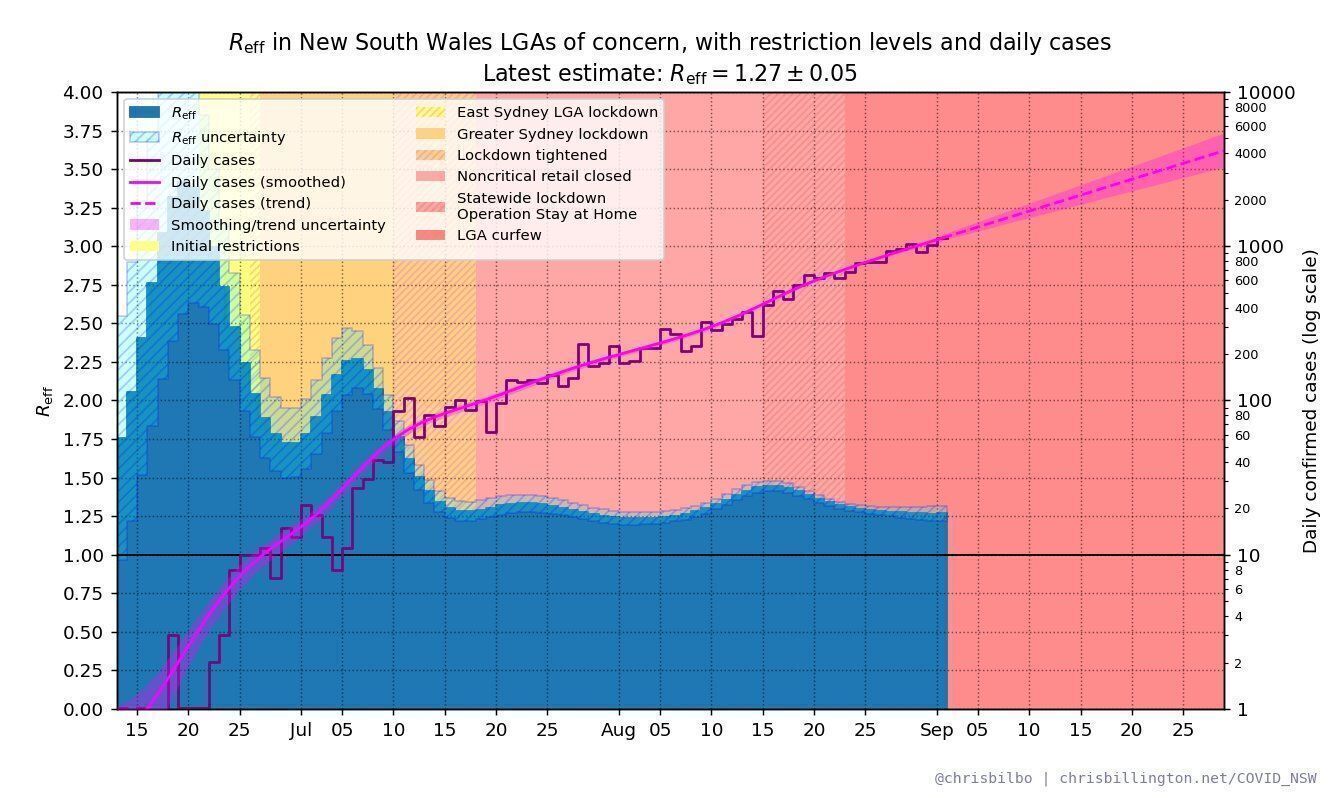
It's now 2021 and I find myself wanting to scream into a paper bag about just how badly Australia has fucked up our response to COVID19. Vaccinations could have been done sooner if they were ordered.
Our two largest cities (Sydney and Melbourne) right now are in a continued state of lockdown, with the various states pursuing a COVID19 eradication strategy which has caused immense social and financial damage to our society. We could be united as country drinking beers right now and I could be with my kids but instead haunting images of police officers assaulting unarmed civilians are traversing through social media.
Let’s check in on liberal democracy pic.twitter.com/KXWnF4LYU6
— Auron MacIntyre (@AuronMacintyre) September 24, 2021
Currently, more than 38,000 Australians are stranded overseas and nobody can leave the country unless you have a rarely granted exemption. The prime minister of Australia threatened jail-time for anyone returning back from India due to concerns about the transmissibility of the Delta strain yet the New South Wales government when there was an outbreak of Delta strain was like "nah, she will be alright mate" and did nothing for weeks.
Every couple of days various state health departments of Australia are pushing out press releases about how their contact tracers are overwhelmed and I'm here all by myself reading actual peer-reviewed publications from other countries where this is not an issue because the appropriate technology was rolled out to assist medical professionals.
This topic is personal. I started authoring this article on Fathers Day and it was too upsetting to finish. Due to the lockdowns, my very young children haven't seen their father in 13 weeks and by the time lockdowns are over it's likely going to be six months since they last saw me. The borders are shut and my family unit is separated by two state governments who can't get their shit into gear. I'm going to miss both of their birthdays and the upcoming school holiday period once again.


If you think these lockdowns are not a concern, I'm going to flat out say it here - you are sitting in an immense position of privilege. Our country is divided between those who can work remotely (the laptop class) and those who cannot. Those who have financial means and those who do not. Those whose family units have not been personally affected and those who have.

It's at this point of the story you are probably thinking, oh god. Who are you Geoff, why should I even listen to you and what is your point? In short, I'm an open-source software engineer who formed a community of researchers around digital contact tracing and our work earned us the LinuxConf Australia community recognition award:
2020 Community Recognition Award
Vanessa Teague, Geoffrey Huntley, Jim Mussared, Richard Nelson and the COVID-Safe Analysis team: For advocating for a better solution for All Australians and upholding Linux Australia’s Values.
https://linux.org.au/about-us/awards/
Greg Hunt, the Minister for Health and Aged Care was also quite a big fan of my work, well that is until I started speaking with the media and publicly retracted my support for the application due to breaches in the privacy legislation that underpinned the entire program of work were ignored.
"I've seen overnight some of the best technical minds in the country have been independently going through the #covidsafe app"
- Greg Hunt
From that point onwards, a dirty game of cat-and-mouse appeared where my previous vouch of the application was used against me by the DTA every time I spoke with the media. As the saga evolved accredited members of the media also received the same disdain and form letter responses.
Not super impressed with this form response I got from DTA when I sent them specific issues with the app raised by developers. pic.twitter.com/5KdiPBTlbz
— Josh Taylor (@joshgnosis) May 7, 2020
As this post continues I hope you identify the recurring theme here that there have been fundamental problems with how the Australian government has engaged with its citizens, industry experts, journalists and where we are now (and our future privacy nightmares) can be in part traced back to the bungling of COVIDSafe.
what is COVIDSafe?
COVIDSafe is a digital contact tracing app announced by the Australian Government on 14 April 2020 to help combat the ongoing COVID-19 pandemic. The app was based on the BlueTrace protocol, originally developed by the Singaporean Government, and was first released on 26 April 2020.

The app was intended to augment traditional contact tracing by automatically tracking encounters between users and later allowing a state or territory health authority to warn a user they have come within 1.5 metres was completely ineffective at doing due to inappropriate technology choices, technical implementation flaws and failure to develop a social license.
at first, it was just me and matthew
On the 26th of April, I started dissecting the application and it quickly rose to the top of HackerNews and Mike Cannon Brookes (Co-founder of Atlassian) posted his first-ever comment on the website in response:
[snip] They won’t get it all right - and we as a tech community can help them. Find a bug & help get them closed.
- Mike Cannon Brookes
Meanwhile, my friend Mathew Robbins also was pulling apart the application in search of answers:
Also, my good friend @GeoffreyHuntley is doing a much more thorough tear down of the app.
— Matthew Robbins (@matthewrdev) April 26, 2020
See here: https://t.co/1RhDvtdFTH
Both Michael and I were perplexed that a piece of technology was being launched at a press conference by ministers of the Australian government and there was no one made available to answer questions about the technology. Not a single technologist was in sight.
As there was no technologist provided to answer questions from the media, sourcing of experts was left up to the media and the result was chaos where the experts were spouting assumptions or what they heard in the press conference.
No one who was speaking with the press had actually looked inside the application and the applications source code was not made available so without consideration of legalities I published the decompiled source code of the application on GitHub
and with the help of others we called our own press conference:
then came community
The biggest piece of advice I can share with anyone getting involved with Australian politics is to not be a single person. I'm forever grateful to the unnamed academic who pulled me aside in the early days to teach me this lesson. Form a community, be the lone dancing idiot at first but when smarter people turn up do everything you can to support and focus the spotlight that was once on you on them instead.
As a result of running our own press conference three heavy hitters turned up in the newly formed discord server and from that point onwards my role changed from being the lone dancing person to the person who was declining media interviews so that Jim, Richard and Vanessa would get air-time.
Jim Mussared

Jim is a hybrid hardware and software developer, with current professional experience with open-source development and designing/developing BLE-based products for George Robotics. Formerly worked in programming/electronics education at Grok Learning, and before that at Google Australia as a tech lead in the SRE team as well as some time working with the Android team.
Jim's Bluetooth research into contact tracing has received worldwide praise. Jim discovered a Bluetooth security vulnerability (CVE-2020-12856) which requires governments to modify their technological approaches and programs of work
Richard Nelson

Richard is a professional software engineer of 16 years, 8 of which have been in mobile app development and leadership where he managed 6 squads, consisting of 32 developers at Qantas. Richard has a strong interest in InfoSec, and his research into the iPhone application background behaviour identified a coding error as a contributing factor preventing COVIDSafe from working effectively. Richard also discovered a denial of service vulnerability (CVE-2020–12717) in COVIDSafe.
Vanessa Teague

Vanessa Teague is an Australian cryptographer, known for her work on secret sharing, cryptographic protocols, and the security of electronic voting. She is Associate Professor (Adj.) at the Australian National University. Her work has uncovered serious errors and security problems in e-voting and e-counting systems in Western Australia, New South Wales and Switzerland. The problems identified allowed for undetectable privacy breaches or election manipulation.
#AusOpenTech
The topic of COVIDSafe is pretty much done and dusted these days but it served as a melting point that brought us four together. These days you'll often find us and others publishing research as AusOpenTech:
I'm kicking off 2021 by starting a conversation about how Aus could build better open government tech.
— Vanessa Teague (@VTeagueAus) January 1, 2021
Help me make a plan https://t.co/ybf7t3rKZb
We can borrow some ideas from https://t.co/AYrCc7PFiO@jim_mussared @noneuclideangrl @GeoffreyHuntley
Who else is in? #Auspol
our latest publication
I finally got a more complete version of a COVIDSafe report the govt seemed to be desperately hiding. It showed warnings about the app's ineffectiveness as early as Dec '20 in a draft report and March '21 in the final. Story below 👇🔓 v @canberratimes https://t.co/7Az7ZY05u6
— Sarah Basford Canales (@sbasfordcanales) August 28, 2021
In response to the heavily redacted report released by the Australian government last month, we released our own report which used factual information presented in the Government’s report, along with known technical capabilities and limitations of the application in order to make recommendations for future work.
.png)
We also compared more thoroughly with other technical solutions used globally, in particular Google and Apple’s collaboration on their Exposure Notification Framework (GAEN). The intended audience of the report are people who want to have an understanding of the history and issues that the COVIDSafe app faced with regards to functionality, security and privacy, and those who wish to learn from these challenges that the development of the COVIDSafe application faced.

find a bug & help get them closed
The initial problems that were discovered by the community ranged from identifying misconfigured firewalls that inhibited people from completing registration in the application if they were connected to WiFi (yes, seriously) to missing telecommunication infrastructure:
We identified a screen in the application that would likely cause panic:
When a user taps the "upload my data" button the next screen asserts "You have tested positive for COVID-19" which may be a false assertion and cause confusion. This text needs changing. Since the user is only supposed to upload data when asked to by a health official (see the previous screen), this statement should reiterate that data should not be uploaded UNLESS you have tested positive. It’s possible that uploading data without having tested positive will result in unnecessary and false notifications being sent to other users
This problem was reported to the DTA on launch night and on the 28th of April it happened:
breach of privacy legislation
As days went past, we discovered that the application had a number of issues that allowed a malicious person to track any user for an indefinite period of time and the application was in breach of the privacy legislation that underpinned the program of work.
Here's a demonstration of Issue #4 in action. The notification is injected into the app, but the data is not. Both the Z2 and this device are on the latest versions of COVIDSafe. pic.twitter.com/17nszAoHNr
— Richard Nelson (@wabzqem) May 5, 2020
After numerous attempts by the community to contact the federal department of health, the digital transformation office and 1300 CYBER1 we turned to the media as there was (and continues to be) no vulnerability disclosure program.
As a result of ABC Radio National broadcast and Isobel Roe's help the DTA finally picked up the phone and called us. We now had a direct line to a public servant in leadership that we could speak directly with if we need to escalate (eg security research that's wormable) and discussions were had with assurances provided that the privacy problems would be resolved.
the first software update
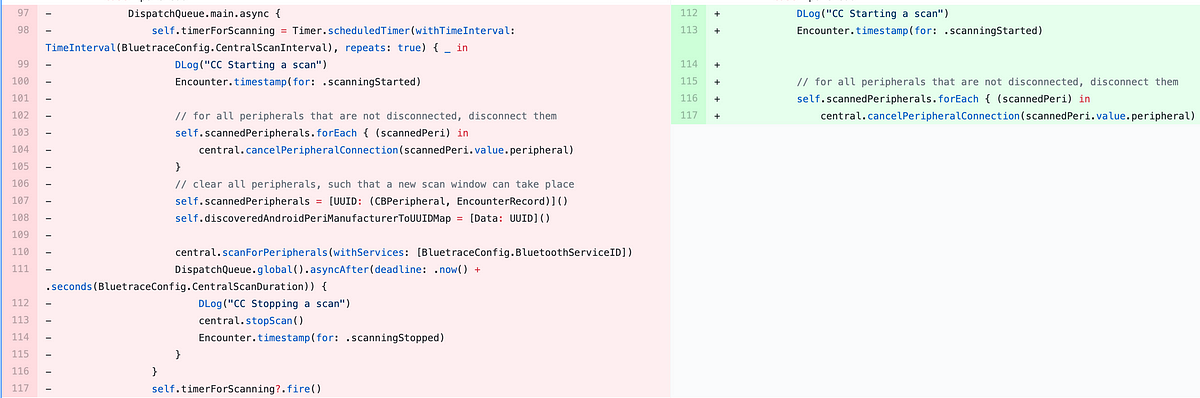
I was in the middle of driving my kids back home across the QLD / NSW border when the update was released. The team quickly decompiled the application and uploaded it on top of the existing source code on GitHub to generate a diff.
The update was visual changes only - a new coat of paint.
None of the privacy flaws were resolved and we had been waiting weeks for this update. COVIDSafe was caching a characteristic value that was read by a remote device using the MAC address of the remote device. Due to a logic error, this cache was only cleared when a successful transaction takes place (i.e. the remote device subsequently writes its own payload back to the characteristic).
Importantly, the cache entry was not removed when:
- The two-hour expiry finishes for the TempID
- After any sort of short time limit.
This meant that a remote device using a static address that never completed the transaction will always see the same cached TempID. This cached value lasted until the app is restarted (likely due to a phone reboot). This flaw also existed in the version of the OpenTrace source code that was shared with the Australian team and was been inherited by the Australian app.
The issue was first reported to the Singapore OpenTrace team at 12:38 am on 30/04/2020 and was fixed in this commit to the opentrace-android repository at 7:11pm on the same day.
The issue was first reported to privacy@health.gov.au at 1:19 am on 27/04/2020, and subsequently by in-app feedback later that day. It was also reported to asd.assist@defence.gov.au at 4:52 pm on 27/04/2020 and was finally fixed seventeen days later on 14/05/2020
remote control of mobile phones
On May 5th, 2020 both Jim Mussared (George Robotics) and Alwen Tiu (The Australian National University) responsibility disclosed a critical security vulnerability to the Australian government and put themselves under a self-imposed embargo due to the severity.
This vulnerability enabled permanent tracking of people even after they had uninstalled the COVIDSafe application and remote control of mobile phones whilst it was installed.
On the 19th of June 2020, the prime minister of Australia called a mysterious presser that Australia was under cyber attack. At the time details were scarce but we now know it was related to unpatched Telerik controls.

This presser is memorable for the AUSOpenTech community because the government and corporates were pushing for Australians to "download the app" and in doing so was exposing 6 million Australians who had installed the application to be remotely controlled and audio intercepted if the attacker was in Bluetooth proximity. For all the hoo haa about a cyber attack, the government and corporations were pushing people to install software onto their phones which enabled cyber attacks. 🤦
Um. Hungry Jack’s just encouraged everyone to download COVIDSafe pic.twitter.com/1uE62TY3uJ
— Ben Grubb 🐛 (@bengrubb) May 11, 2020
During the self-imposed embargo by Jim and Alwen, they continued their research and were madly sending messages via LinkedIn to government employees in other countries which had also adopted the Singapore application. Countries affected included: Singapore, Australia, Morocco, Alberta and Poland to name a few.
Here's how the exploit worked:
- COVIDSafe runs both as a client and server on your handset.
- The client aspect of the application searches for servers around you and connects to them.
- The client asks if the server is COVIDSafe and trusts the server is not hostile.
- A malicious attacker says "hell yeah, I'm COVIDSafe" and then COVIDSafe does full Bluetooth device pairing.
- Now that the victim is paired with the malicious attacker the Bluetooth profile is then switched to become either a network adapter (intercept network traffic), a keyboard/mouse (enter input/remote control) or an audio device (hijack audio and microphone).
It's that simple. COVIDSafe trusted client input. Security exploits are rated out of a scale of 10 - this one came in at a whopping 9.8:

bluetooth used incorrectly
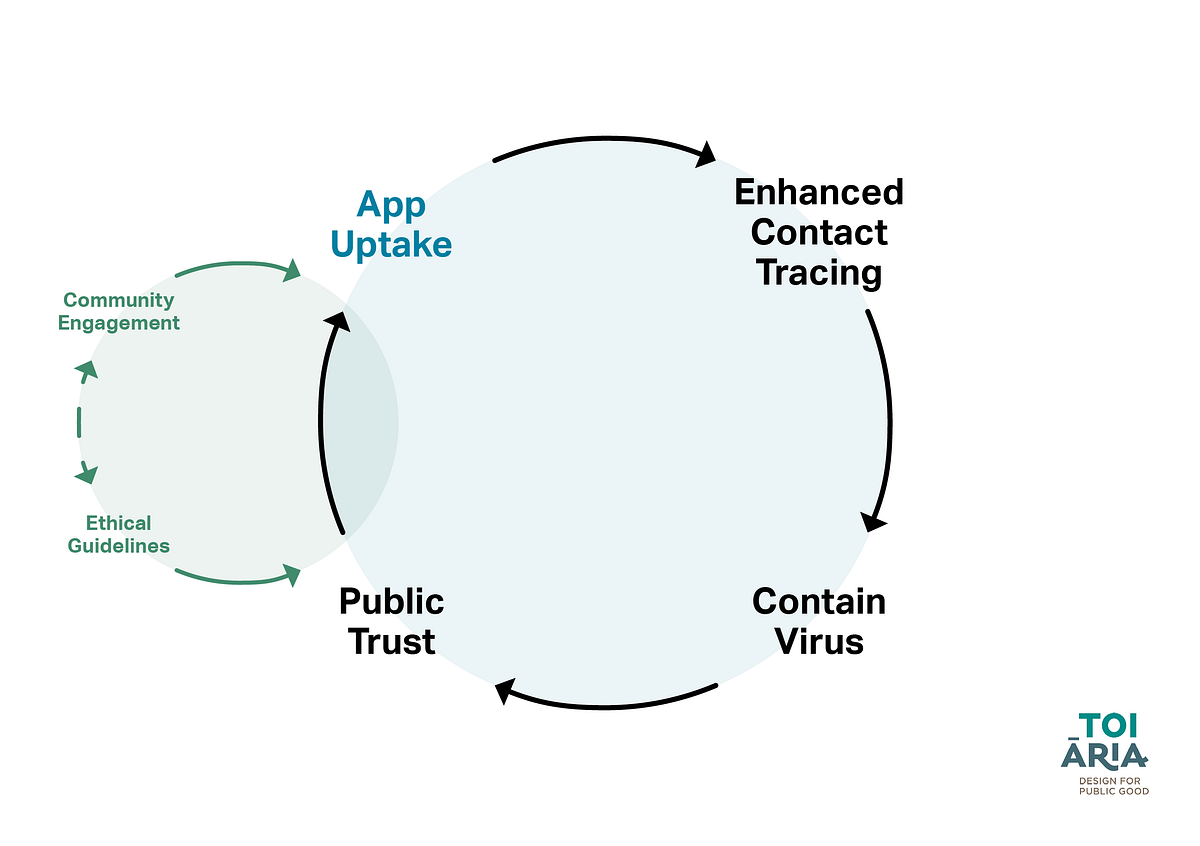
This vulnerability and the privacy flaws discovered by the community existed because Australia is using Bluetooth in a way it was never designed to be used. Google and Apple because they designed the handsets that we use day-to-day knew this and collaborated by releasing the Exposure Notification Framework (GAEN).
One of the fundamental differences between GAEN and the Bluetooth pairing approach used by Australia is that GAEN is constant in space and time whereas Bluetooth pairing is quadratic in space in time.
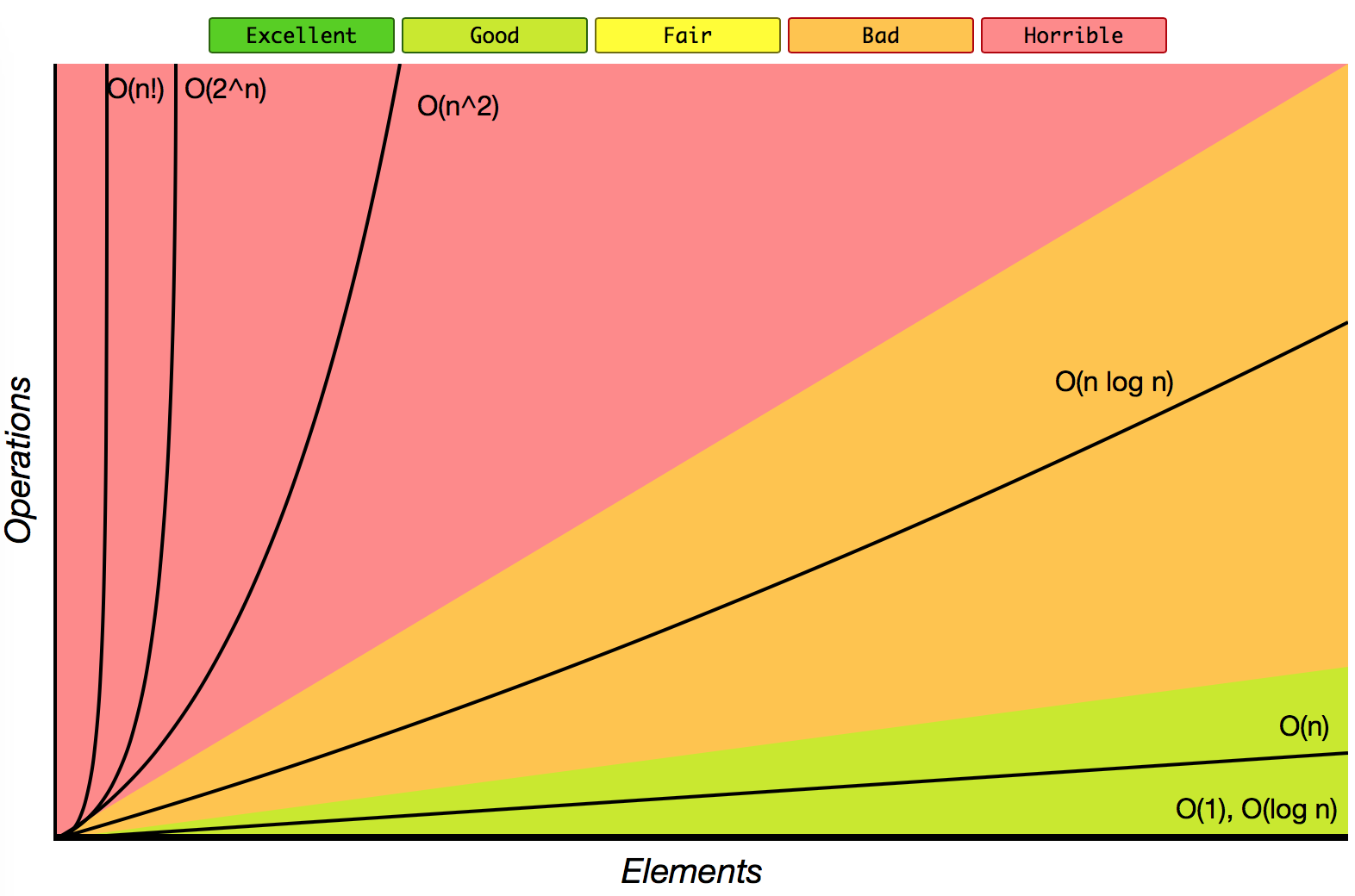
Fundamentally this means that the more people that you are around the more that the effectiveness of COVIDSafe degrades. Yes, that's right the approach taken by Australia means contact tracing becomes more ineffective the more people you are around whereas the GAEN approach hums along without a hitch.
Want to go to the footy?
— Greg Hunt (@GregHuntMP) May 2, 2020
Download the app.
Link - https://t.co/vn3NoeQpal pic.twitter.com/qhwuz9kQAY
In addition to this most mobile phones when scanning for devices to pair to (other COVIDSafe users) cannot maintain existing connections when doing a scan. Thus fundamentally explaining why people were experiencing dropouts with their Bluetooth headphones, disconnects from their Apple Watches
I noticed my Apple Watch kept disconnecting from my phone. As soon as I killed Covidsafe it worked again. Huh.
— Josh Taylor (@joshgnosis) May 20, 2020
and why diabetes Australia put out that warning...

These problems would not have existed had Australia chosen the Exposure Notification Framework (GAEN) path.
iPhone
There's too much to say on this topic. The application was never going to work because fundamentally the client and server aspects of COVIDSafe run as part of the userland and on iOS user applications terminate when they move into the background. The only reason the application even got to a semi-workable level is thanks to the work done by Richard.
Again this problem would not have existed had Australia chosen the Exposure Notification Framework (GAEN) path.
senate
I submitted multiple submissions to the Australian Senate but they were rejected. Jim submitted to the Australian Senate but it was not accepted until the findings of the senate were concluded thus it is likely no senators read his research even though he is the #1 expert in Australia on how the application works.
DTA has been misleading the public about the Covidsafe app. The documents tabled in the senate prove that. pic.twitter.com/aGnggip76k
— Josh Taylor (@joshgnosis) June 16, 2020
the daily presser







One of the most fundamentally annoying frustrating things about how the Australian government has responded to the COVID19 pandemic is the over-reliance on pressers. The daily presser has become a meme in itself.

Instead of putting the information that people need on peoples phones in the COVIDSafe application everyone in Australia has had to tune into regularly scheduled TV broadcasts. What if instead, the COVIDSafe application had actual utility and provided reasons for people to open it:
- Amount of daily cases in your local area.
- A map displaying where known cases are.
- Information about border restrictions.
- Directives if you need to isolate.
- Provided a way to book vaccinations.
- A map displaying places where you can get vaccinated.
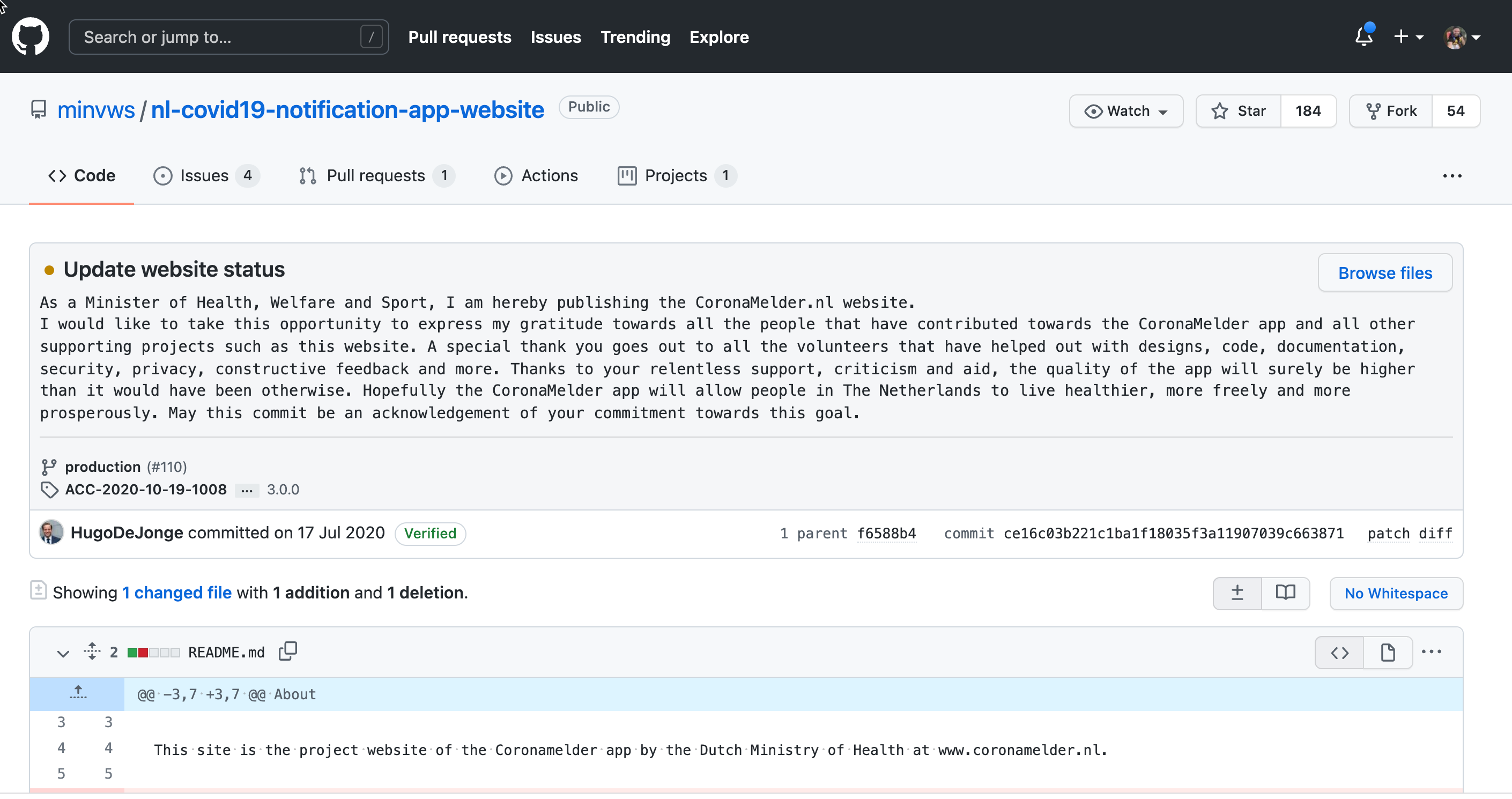
research the Netherlands
If you are an academic reading this page then I highly recommend researching the drama in the Netherlands. Initially, the Dutch government started heading down a path similar to Australia but managed to do a massive course correction and ended up being the international north star in digital contact tracing.
The Dutch government ditched giving away free pizzas at hackathons (and getting submissions containing pirated intellectual property from companies) and instead turned to and enabled their technology community. The mastermind behind turning towards and enabling the hacker community was Ron Roozendaal:
Dit weekend werd CoronaCheck veel meer gebruikt. De afgelopen tijd werd mij veel gevraagd waarom ik er aan meewerk. Jij, Ron, bent immers zo gespitst op privacy? Met alle vragen van de afgelopen weken geef ik in een nieuwe blog iets meer kleuring. https://t.co/jrIsruMb5K
— Ron Roozendaal (@Ron_Roozendaal) September 26, 2021
The Dutch minister of health did a public AMA and committed the source code of their application to GitHub! 😍
1/2 Nederland onderzoekt of het mogelijk is om met een app anoniem de contacten te waarschuwen die iemand met Corona zich niet herinnert of niet kent. In alle openheid. Zowel de eerste broncode van de apps als van de backend staat nu online. https://t.co/vxW9qclXhP
— Ron Roozendaal (@Ron_Roozendaal) June 3, 2020
further reading
If you want to dig deeper into COVIDSafe then I recommend reading the following:
- https://roycekurmelovs.substack.com/p/crackingcovidsafept1
- https://roycekurmelovs.substack.com/p/crackingcovidsafeqz
- https://roycekurmelovs.substack.com/p/crackingcovidsafept2
- https://roycekurmelovs.substack.com/p/crackingcovidsafept3
- https://roycekurmelovs.substack.com/p/crackingcovidsafeqandadw
- https://roycekurmelovs.substack.com/p/crackingcovidsafept4
- https://roycekurmelovs.substack.com/p/crackingcovidsafeqandavt
- https://roycekurmelovs.substack.com/p/crackingcovidsafept5
- https://roycekurmelovs.substack.com/p/crackingcovidsafept6
- https://roycekurmelovs.substack.com/p/crackingcovidsafept7
- https://github.com/AusOpenTech/COVIDSafe-Report/blob/main/Report on the operation and effectiveness of the COVIDSafe application.pdf
- https://www.aph.gov.au/DocumentStore.ashx?id=f5744df4-0c60-42d6-9958-cfad3d5c4110&subId=699894
- https://github.com/vteague/contactTracing/blob/master/blog/2020-07-07IssueSummary.md
- https://emmablomkamp.medium.com/a-crisis-is-not-an-excuse-841f575356c1?source=friends_link&sk=54515e8dc63c2d86132090fcfd6f2ccf
- https://docs.google.com/document/d/1u5a5ersKBH6eG362atALrzuXo3zuZ70qrGomWVEC27U/preview#heading=h.q4sovraiy4kn
final remarks
I recently had the privilege of doing a guest lecture at an Australian university on COVIDSafe and it goes without saying that I'm always happy to chat with anyone about anything technology related so if you are wondering, the answer is yes. Just ask.
I got involved with COVIDSafe ultimately because I deeply believe that:
Medical professionals (contact tracers) deserve technical tools that work. Forcing them (via political pressure) to use ineffective tools robs them of precious time which could be better spent contact tracing.
These days I don't think much about the COVIDSafe application anymore as it's dead in the eyes of politicians and the Australian public. Each state now has their own check-in application and the information collected is not protected by the excellent federal legislation that governs the COVIDSafe application.
How it started - Jun 12, 2020
— geoff 💉💉 (@GeoffreyHuntley) September 26, 2021
How it's going - Today
"Businesses are subject to being shut down and slugged with an $11,000 fine if they allow entry to an unvaccinated person [and check-in apps are mandatory]" https://t.co/q9lzDmhXmH pic.twitter.com/jGxMzXP1ET
I guess I'll close by saying all of the QR code functionality that is being rolled out right now could have been deployed into the COVIDSafe application and we wouldn't have had these privacy issues:

The contact tracers in Australia's state health departments of Australia's contact tracers didn't need to be overwhelmed and if leadership had chosen the correct technology they would have been able to be more effective:
.png)

Thanks for reading.
ps. The Australian Government needs a Vulnerability Disclosure Policy. I would love nothing more than to be able to deal directly with engineers and have sound knowledge that critical problems will be fixed vs having to interface with the media to get problems resolved.

In which @GeoffreyHuntley writes up the 💯 work he, @VTeagueAus, @wabzqem and @jim_mussared did on forming a community around #CovidSafe app with the intent to make it better 👏
— Kathy Reid is 💉💉 two shots good (@KathyReid) September 26, 2021
Where would we be now if the gov't had worked with, not against, some of tech's brightest? 🤔 👇 https://t.co/XvCsq4E3W3