the z80 technique reveals the source code for Atlassian's 'rovo' AI assistant
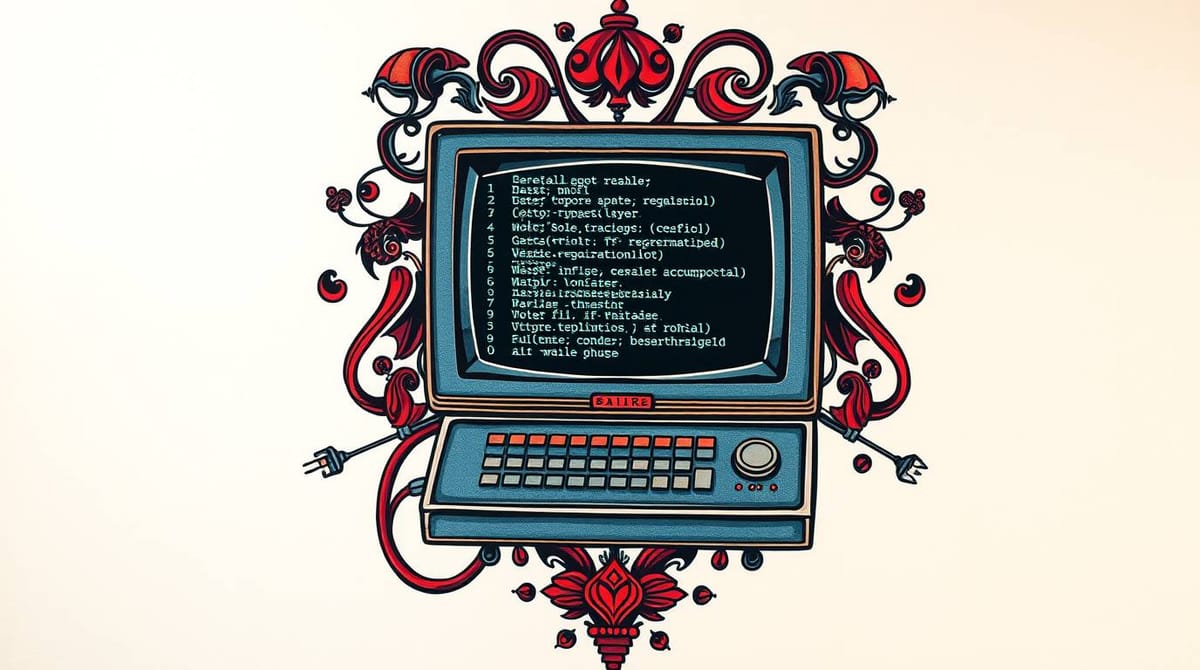
Ever wondered what happens if you take the technique at "Can a LLM convert C, to ASM to specs and then to a working Z/80 Speccy tape? Yes." and run it against the Atasslian Command Line (ACLI) interface? Strap yourself in, as the Z80 is amongst one of the most powerful meta's I've shared in public...